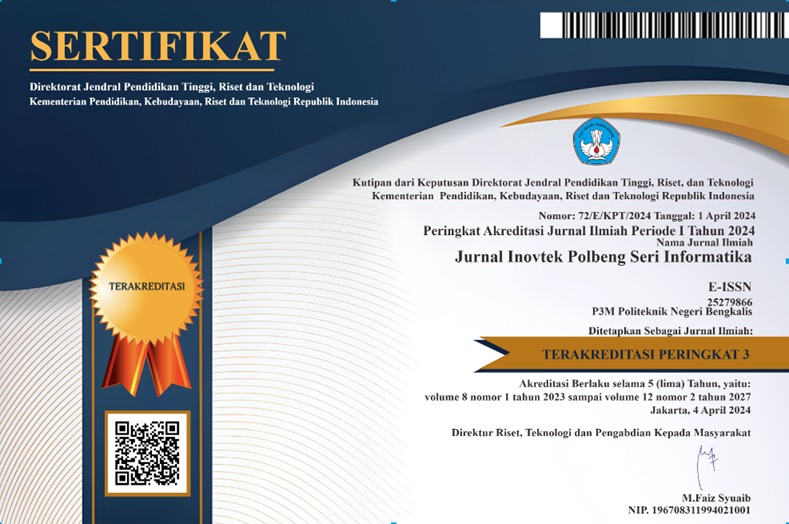
Implementation of a Network Security System Using the Port Knocking Method at Taruna Satria Vocational School Pekanbaru
DOI:
https://doi.org/10.35314/f5pjjj80Keywords:
Keamanan Jaringan, Port Knocking, Port Scanning, Brute Force, DDoSAbstract
SMK Taruna Satria Pekanbaru utilizes its network for teaching and school administration activities. However, security issues have led to incidents where intruders gained access to the MikroTik webfig and altered configurations, such as changing hotspot passwords and adding unauthorized user profiles. Initial data shows that the network experienced up to a 30% performance drop due to illegal access, with a high potential for attacks, especially on HTTP (80), SSH (22), Telnet (23), and Winbox (8291) ports if left open. To address these issues, the Port Knocking method was implemented, which hides ports and only allows access to users who knock on the ports in a specific sequence. Legitimate users must knock on the ports in a designated order to activate access, which then adds their IP address to the whitelist. Access to services is granted only if the correct knocking sequence is followed within a specific timeframe. Testing through simulations of Port Scanning, brute force, and DDoS attacks has demonstrated this method’s effectiveness in hiding ports from scanning detection and reducing brute force and DDoS attack risks. Although effective, this method relies on accurate configuration patterns. Implementing Port Knocking is expected to enhance network security and reduce unauthorized access risks at SMK Taruna Satria Pekanbaru.
Downloads
Downloads
Published
Issue
Section
License
Copyright (c) 2024 INOVTEK Polbeng - Seri Informatika

This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License.